Security and AI services built for business-critical environments
We connect cyber security, AI-focused risk controls, and endpoint operations in one accountable delivery model, designed for enterprise scale and executive visibility.
What enterprise buyers expect
- Clear ownership between IT, security, and business teams
- Measurable service quality with KPI and KRI visibility
- Defensible documentation for leadership and audit stakeholders
A structured portfolio with clear business impact
Existing capabilities are preserved, then reorganized into a faster decision journey for leadership teams.

Mobile Device Management (MDM) as a Service
Android Enterprise and iOS enrollment services with Zero-Touch, Device Enrollment (DEP/ADE), and optional PointMobile advanced feature integration.
Our delivery model keeps Android enrollment cross-OEM and adds PointMobile-specific advantages only where they provide measurable operational benefit.
View Service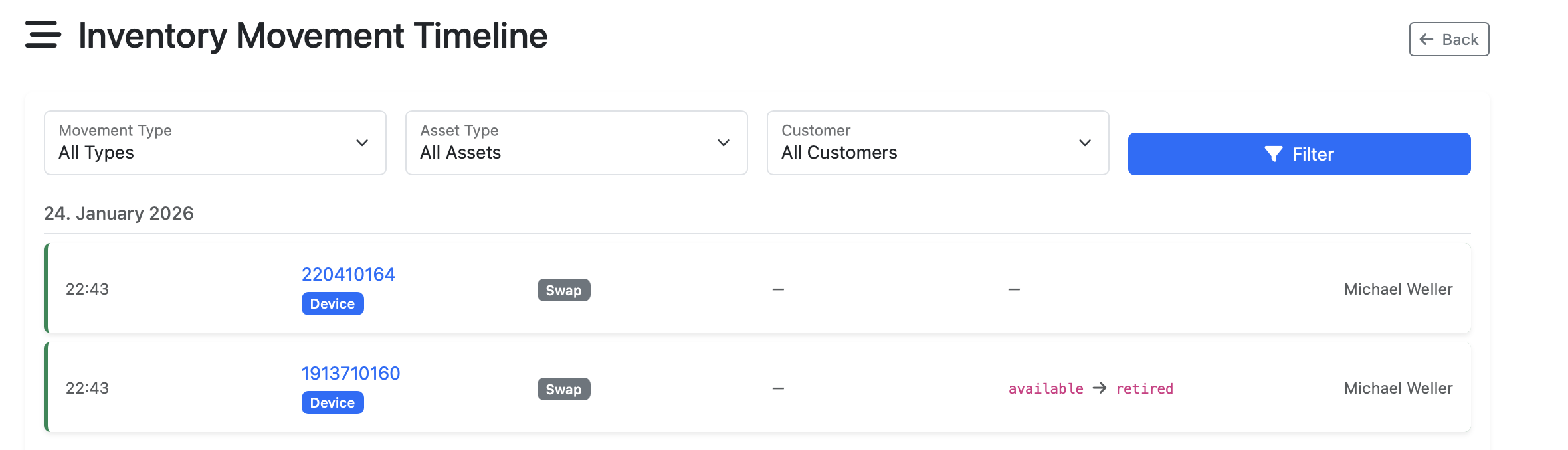
Asset Database
Independent, vendor-neutral asset management for devices, batteries, and cradles.
Built for operations teams who need to maintain asset history across disconnected systems.
View Service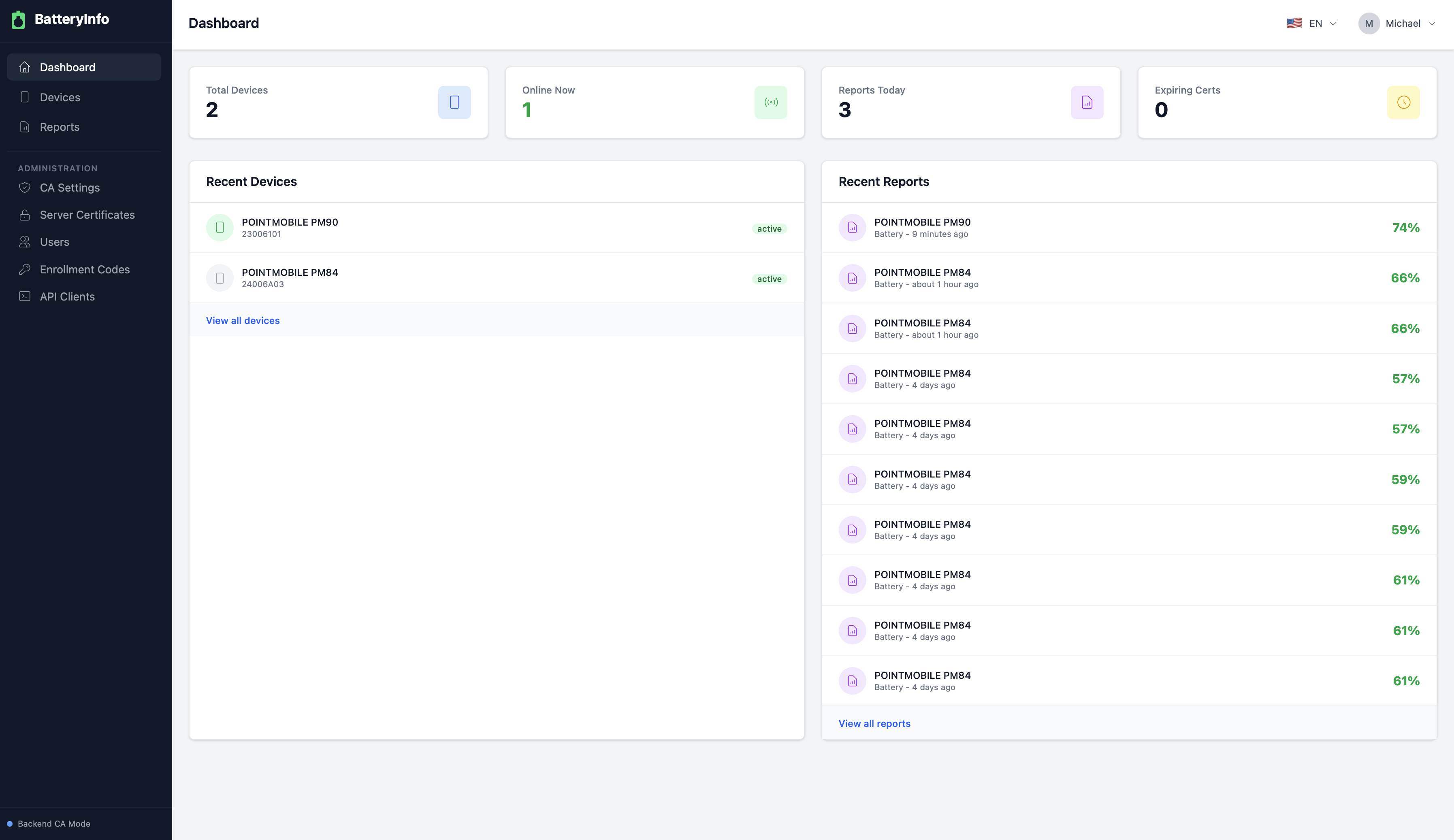
Battery Management System
Real-time battery monitoring, managed enrollment, and predictive maintenance for enterprise fleets.
Designed to help service and operations teams prevent downtime before users are affected.
View Service
Transcriptor
Secure speech-to-text transcription for calls, meetings, and operational documentation.
Built for teams that need clean, reusable transcripts without adding friction to daily operations.
View Service
Cyber Security Services
Enterprise security architecture, hardening, and governance for business-critical environments.
Delivered by teams who work directly with IT operations and security stakeholders.
View Service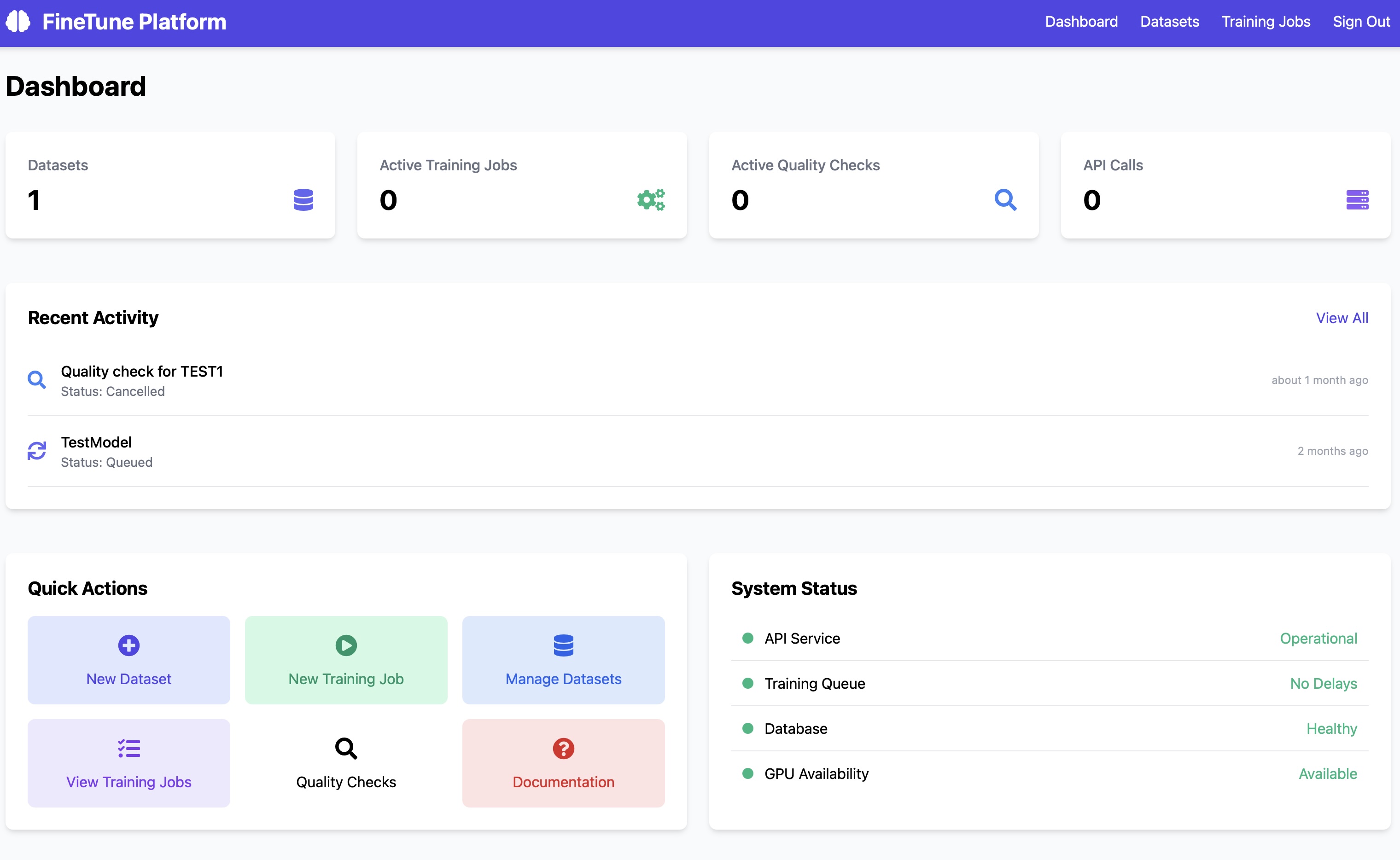
AI Solutions
Local AI training and private model deployment for process optimization with high-sensitivity data protection.
Built for business and engineering teams that need AI value while keeping high-sensitivity enterprise information protected.
View ServiceFrom assessment to monitoring in four controlled phases
Assessment
We evaluate risk exposure, operating maturity, and technical dependencies to establish a defensible baseline.
Roadmap
We prioritize initiatives by impact and effort, with explicit owners, milestones, and measurable targets.
Implementation
We execute technical and organizational changes through controlled rollout and documented standards.
Monitoring
We continuously track performance, risk signals, and improvement opportunities to sustain outcomes.
A clear path from first conversation to operational outcomes
We guide stakeholders from service clarity and trust signals to an actionable project scope.